Overview of Windows/Internet Explorer Security Patch
Microsoft has advised Windows/Internet Explorer users to install an “emergency” out-of-band security patch (i.e. not released on patch-Tuesday) for a recently detected Zero-Day-Exploit (i.e an exploit that has already been actively used prior to the release of the patch).
A security flaw in some versions of Internet Explorer could allow an attacker to remotely run malicious code on an affected device. A user could be stealthily infected by visiting a malicious web page or by being tricked into clicking on a link in an email. “An attacker who successfully exploited the vulnerability could take control of an affected system,” said Microsoft.
Microsoft also issued a fix for its in-built malware scanner Windows Defender, which if exploited, could have triggered a denial-of-service condition resulting in the app failing to work.
Technical Details
| Application Affect: | Internet Explorer 9, 10 and 11 |
| Security Advisory: | CVE-2019-1367 |
| Link to Mitre Advisory: | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-1367 |
| Link to NIST Advisory: | https://nvd.nist.gov/vuln/detail/CVE-2019-1367 |
| Link to Microsoft Advisory: | https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2019-1367 |
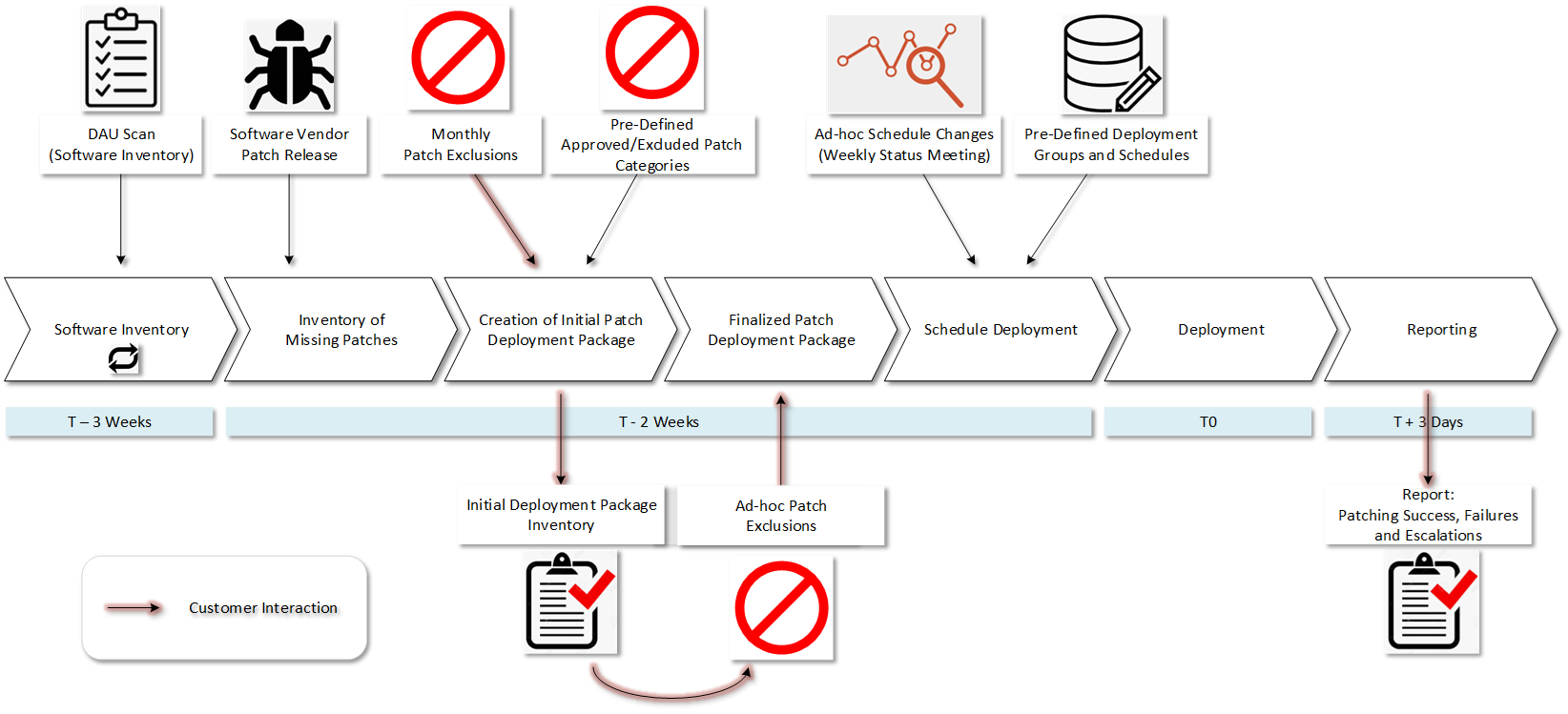
As a Patchworx Client…
We are always working, 24x7x365, to make sure your systems are patched and secured. Our valued Patchworx clients received the below message from us shortly after the Microsoft advisory.
IF you are a customer with Patchworx for Workstations AND…
Have a “24x7” patching schedule (i.e. deployment of software update packages once a week on a 24 x 7 cycle) THEN…
- Alvaka has updated your latest workstation software update package to include the necessary patch for this vulnerability.
- Your users will receive the patch once connected to an internal network or the internet. The workstation will automatically reboot itself within 24 hours of receiving the patch to fully enable its capability.
- It is therefore recommended that you notify all staff members to turn on their workstations and leave them connected to the internal network or internet so that they receive the software update package in a timely manner.
DO NOT have a “24x7” patching schedule (i.e. non-continuous deployment of software update packages. Ex: Deployment of software update packages during a one-week period once a month) THEN…
- Alvaka will be reaching out to you shortly to schedule an out-of-phase software deployment.
IF you are a Patchworx for Servers Customer THEN…
- Alvaka will be reaching out to you shortly to determine which servers are at risk and to schedule an out-of-phase software deployment where necessary.