Third-Party Applications
Software Patching
Threat of Third-Party Applications
If left unpatched, each instance of software is a potential attack vector into your network.
It is standard practice for companies to patch operating systems (OS), and many believe that this is sufficient when it comes to their entire patching process. However, there are still lots of organizations struggling to keep their systems up-to-date, particularly when it comes to software outside the OS.
Organizations of all sizes utilize a diverse set of third-party applications—sometimes tens of thousands of instances—for daily business operations. Reliance on this third-party software, and secure browsers for cloud accessibility, is putting end user machines at risk and poses a greater threat to networks than operating systems. In fact, it is reported that 86% of vulnerabilities come from third-party applications (National Vulnerability Database).
Patchworx Solution
Many applications and browsers have auto updaters to ensure software is up-to-date, however, these updaters can break, or might require user approval or reboot. Plus, applications like Google Chrome, Adobe Flash and Reader, Oracle Java, and Firefox are the applications and browser add-ons that hackers seem to target the most. The only way to be sure that that third-party vulnerabilities are closed, and to decrease your risk of downtime, is to centrally manage the updates and ensure broad coverage.
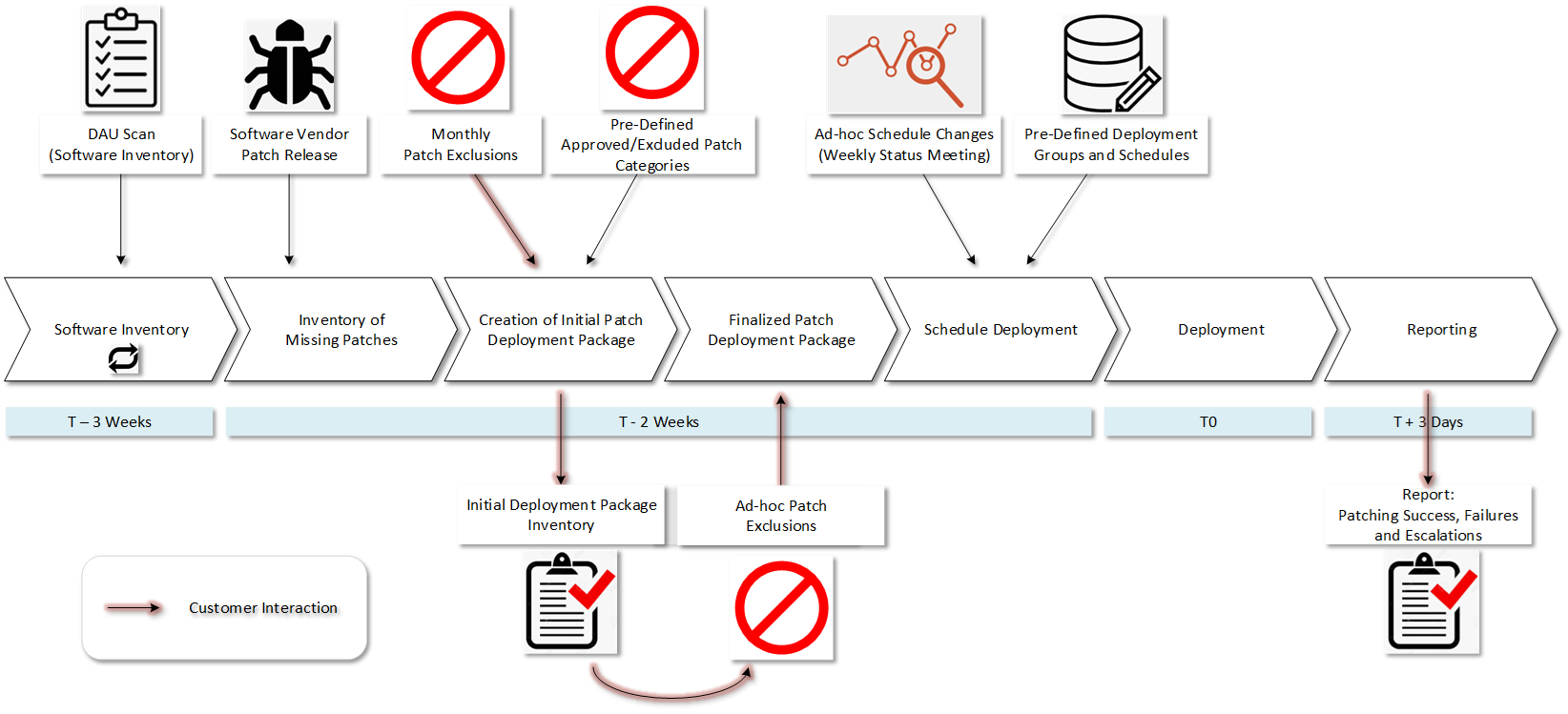
Patchworx is capable of patching hundreds of popular vendors and third-party applications, keeping your systems current with the latest software updates. Patchworx makes patching considerably easier by automating the process of discovering and deploying third-party application patches through the SCCM console.
Features
- Ability to patch hundreds of the most popular applications, including those difficult to install
- Customization of patches to comply with company policies
- Publish patch metadata separately for compliance, audit, or pre-deployment screening
- View and manage all products published to WSUS
- Digital certificate management—re-authorize expired certificates
- Supports authenticating proxies
- Supports disconnected networks
- And much more!